A Spanish-speaking cybercrime gang entitled GXC Team has been seen combining phishing kits with malicious Android applications, extending malware-as-a-service (MaaS) offers to the next level.
Singaporean cybersecurity company Group-IB, which has been tracking the e-crime actor since January 2023, described the crimeware solution as a "sophisticated AI-powered phishing-as-a-service platform" capable of targeting users of more than 36 Spanish banks, governmental bodies and 30 institutions worldwide.
The phishing kit is priced somewhere between $150 and $900 a month, whilst the package combining the phishing kit and Android malware is available on a subscription basis for roughly $500 each month.
Targets of the effort include consumers of Spanish financial institutions, as well as tax and governmental services, e-commerce, banks, and cryptocurrency exchanges in the United States, the United Kingdom, Slovakia, and Brazil. As many as 288 phishing domains linked to the activity have been found to date.
Also part of the scope of services given is the sale of stolen banking credentials and custom coding-for-hire schemes for other cybercriminal groups targeting banking, financial, and cryptocurrency businesses.
"Unlike typical phishing developers, the GXC Team combined phishing kits together with an SMS OTP stealer malware pivoting a typical phishing attack scenario in a slightly new direction," security experts Anton Ushakov and Martijn van den Berk stated in a Thursday study.
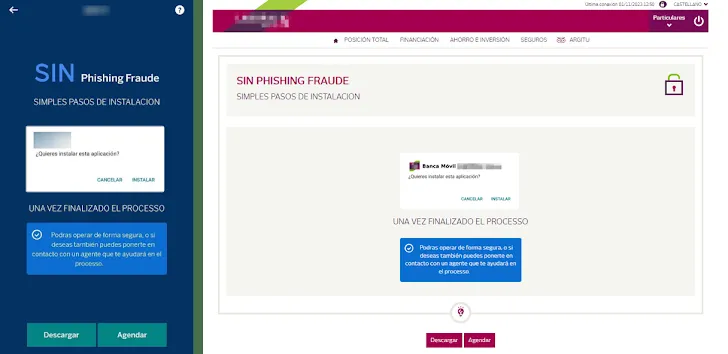
What's significant here is that the threat actors, instead of immediately making use of a fraudulent page to acquire the credentials, push the victims to download an Android-based banking software to prevent phishing assaults. These pages are disseminated by smishing and other techniques.
Once installed, the software seeks for authorization to be configured as the default SMS app, thereby making it feasible to intercept one-time passwords and other messages and exfiltrate them to a Telegram bot under their control.
"In the final stage the app opens a genuine bank's website in WebView allowing users to interact with it normally," the researchers added. "After that, whenever the attacker triggers the OTP prompt, the Android malware silently receives and forwards SMS messages with OTP codes to the Telegram chat controlled by the threat actor."
Among the other services advertised by the threat actor on a dedicated Telegram channel are AI-infused voice calling capabilities that allow its users to generate voice calls to prospective targets based on a sequence of prompts directly from the phishing kit.
These calls generally masquerade as emanating from a bank, ordering consumers to supply their two-factor authentication (2FA) codes, install malicious apps, or execute other unauthorized acts.
"Employing this simple yet effective mechanism enhances the scam scenario even more convincing to their victims, and demonstrates how rapidly and easily AI tools are adopted and implemented by criminals in their schemes, transforming traditional fraud scenarios into new, more sophisticated tactics," the researchers pointed out.
In a recent paper, Google-owned Mandiant disclosed how AI-powered voice clones had the capability to replicate human speech with "uncanny precision," thus allowing for more authentic-sounding phishing (or vishing) schemes that ease initial access, privilege escalation, and lateral movement.
"Threat actors can impersonate executives, colleagues, or even IT support personnel to trick victims into revealing confidential information, granting remote access to systems, or transferring funds," the threat intelligence firm warned.
"The inherent trust associated with a familiar voice can be exploited to manipulate victims into taking actions they would not normally take, such as clicking on malicious links, downloading malware, or divulging sensitive data."
Phishing kits, which also come with adversary-in-the-middle (AiTM) capabilities, have becoming increasingly popular as they decrease the technological barrier to entry for pulling off phishing attacks at scale.
Security researcher mr.d0x, in a paper published last month, said it's possible for bad actors to take advantage of progressive web applications (PWAs) to construct convincing login pages for phishing purposes by modifying the user interface elements to display a phony URL bar.
What's more, such AiTM phishing kits can also be used to break into accounts protected by passkeys on various online platforms by means of what's called an authentication method redaction attack, which takes advantage of the fact that these services still offer a less-secure authentication method as a fallback mechanism even when passkeys have been configured.
"Since the AitM can manipulate the view presented to the user by modifying HTML, CSS and images or JavaScript in the login page, as it is proxied through to the end user, they can control the authentication flow and remove all references to passkey authentication," cybersecurity company eSentire said.
The report comes amid a recent spike in phishing attempts containing URLs that are already encoded using security solutions such as Secure Email Gateways (SEGs) in an attempt to hide phishing links and evade inspection, according to Barracuda Networks and Cofense.
Social engineering attacks have also been observed resorting to unusual methods wherein users are enticed into visiting seemingly legitimate websites and are then asked to manually copy, paste, and execute obfuscated code into a PowerShell terminal under the guise of fixing issues with viewing content in a web browser.
Details of the malware delivery mechanism have been previously disclosed by ReliaQuest and Proofpoint. McAfee Labs is following the behavior under the moniker ClickFix.
"By embedding Base64-encoded scripts within seemingly legitimate error prompts, attackers deceive users into performing a series of actions that result in the execution of malicious PowerShell commands," researchers Yashvi Shah and Vignesh Dhatchanamoorthy explained.
"These commands typically download and execute payloads, such as HTA files, from remote servers, subsequently deploying malware like DarkGate and Lumma Stealer."